Encrypted index
Embeddings, IDs, and metadata stored only as ciphertext — per-record IVs, authenticated. Compromise the disk, read nothing.
CyborgDB keeps inference data end-to-end encrypted — at rest, in transit, and in-use. Build secure enterprise AI on the only encrypted vector store.
Embeddings, IDs, and metadata stored only as ciphertext — per-record IVs, authenticated. Compromise the disk, read nothing.
Payloads are AEAD-encrypted before they ever touch the network. TLS rides on top — but it isn't what's keeping the data safe.
Forward-secure ANN search runs on encrypted index nodes. The server never holds plaintext embeddings or full index keys.
End-to-end encryption and cryptographic access control walk into every audit with the box already ticked.
Proxy mode sits in front of Postgres, Redis, or S3. No migration, no net-new infrastructure.
Each tenant's data is encrypted with their own key. Boundaries enforced in math, not application logic.
Security doesn’t have to mean compromising performance. CyborgDB keeps pace with unencrypted vector databases — and beats most of them.
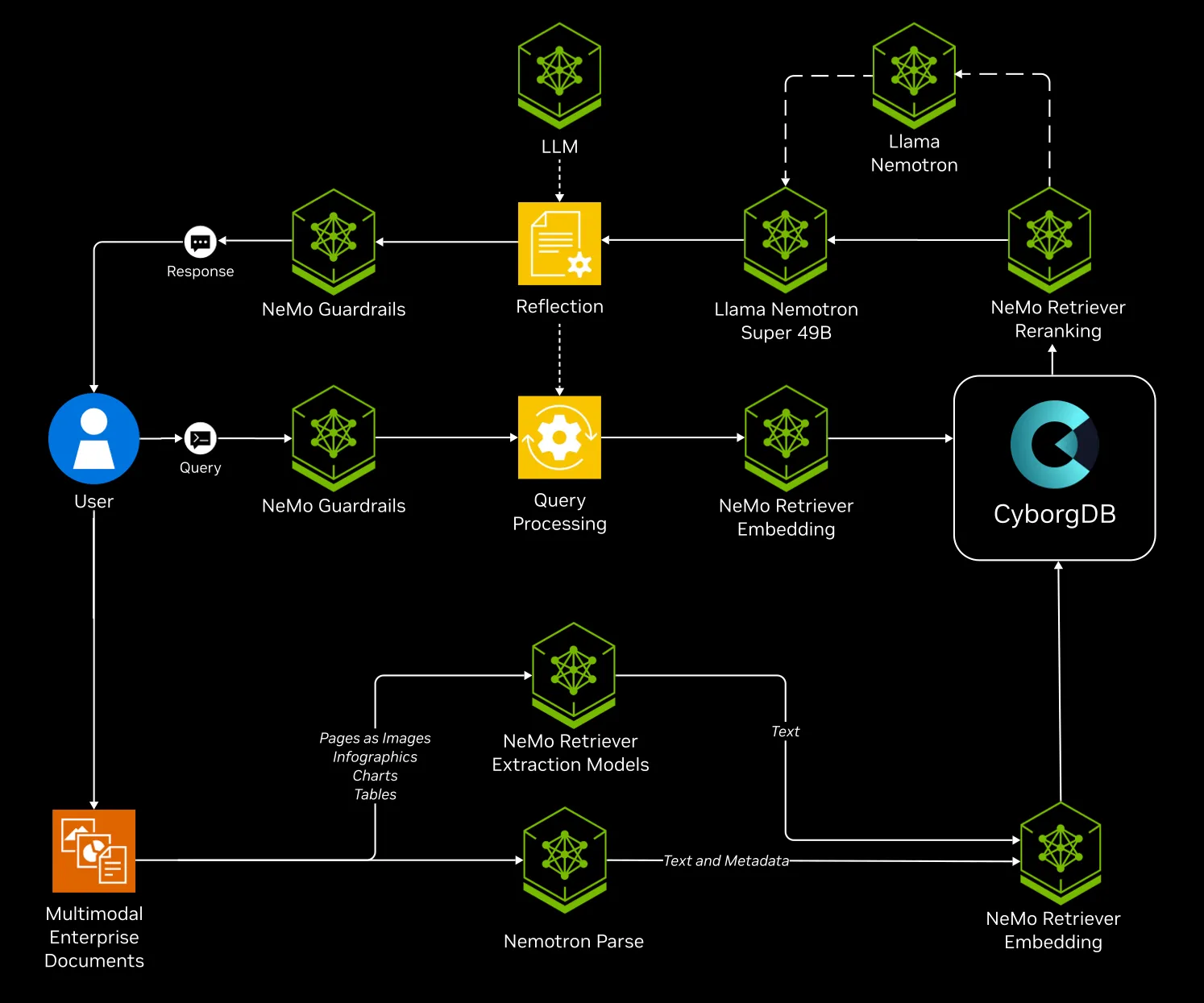
The Cyborg–NVIDIA Enterprise RAG Blueprint is a reference architecture for deploying secure, scalable AI applications. Cyborg is one of just eight companies invited by NVIDIA to author an Enterprise Blueprint.
It combines best-in-class NVIDIA NIMs with CyborgDB to deliver encrypted-in-use retrieval for AI knowledge bases.
One container, one config, one import change. Keep your stack, reuse your data plane, ship to prod the same afternoon.
Free for up to 1M vectors. Compliance-ready from the first query.